Which Protocol Header Would Layer 4 Device Read and Process
The Open Systems Interconnection model (OSI model) is a conceptual model that characterises and standardises the advice functions of a telecommunication or computing system without regard to its underlying internal structure and technology. Its goal is the interoperability of various communication systems with standard communication protocols.
The model partitions the flow of information in a advice organization into vii abstraction layers, from the physical implementation of transmitting $.25 across a communications medium to the highest-level representation of data of a distributed awarding. Each intermediate layer serves a class of functionality to the layer higher up it and is served by the layer below it. Classes of functionality are realized in software by standardized communication protocols.
The OSI model was developed starting in the late 1970s to support the emergence of the diverse computer networking methods that were competing for application in the large national networking efforts in the world. In the 1980s, the model became a working product of the Open Systems Interconnection grouping at the International Organization for Standardization (ISO). While attempting to provide a comprehensive description of networking, the model failed to garner reliance by the software architects in the design of the early Cyberspace, which is reflected in the less prescriptive Internet Protocol Suite, principally sponsored nether the auspices of the Internet Technology Chore Forcefulness (IETF).
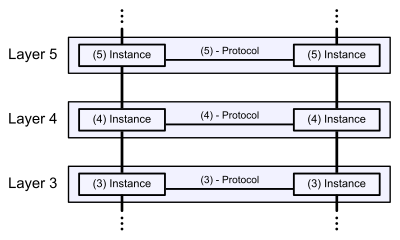
Advice in the OSI-Model (example with layers 3 to 5)
History [edit]
In the early on- and mid-1970s, networking was largely either authorities-sponsored (NPL network in the Great britain, ARPANET in the US, CYCLADES in France) or vendor-developed with proprietary standards, such as IBM'southward Systems Network Architecture and Digital Equipment Corporation's DECnet. Public information networks were only just beginning to emerge, and these began to use the X.25 standard in the late 1970s.[2] [3]
The Experimental Packet Switched System in the United kingdom circa 1973–1975 identified the need for defining college level protocols.[2] The United kingdom of great britain and northern ireland National Computing Middle publication 'Why Distributed Computing' which came from considerable enquiry into future configurations for reckoner systems,[4] resulted in the Uk presenting the case for an international standards committee to cover this surface area at the ISO coming together in Sydney in March 1977.[5]
Beginning in 1977, the International System for Standardization (ISO) conducted a plan to develop general standards and methods of networking. A similar procedure evolved at the International Telegraph and Telephone Consultative Commission (CCITT, from French: Comité Consultatif International Téléphonique et Télégraphique). Both bodies developed documents that divers similar networking models. The OSI model was first defined in raw form in Washington, DC in Feb 1978 by Hubert Zimmermann of France and the refined but nonetheless draft standard was published by the ISO in 1980.[6]
The drafters of the reference model had to argue with many competing priorities and interests. The rate of technological change made it necessary to define standards that new systems could converge to rather than standardizing procedures afterwards the fact; the reverse of the traditional approach to developing standards.[7] Although not a standard itself, it was a framework in which future standards could be divers.[8]
In 1983, the CCITT and ISO documents were merged to form The Bones Reference Model for Open Systems Interconnection, usually referred to as the Open Systems Interconnection Reference Model, OSI Reference Model, or just OSI model. It was published in 1984 by both the ISO, as standard ISO 7498, and the renamed CCITT (now chosen the Telecommunications Standardization Sector of the International Telecommunication Union or ITU-T) every bit standard X.200.
OSI had two major components, an abstract model of networking, chosen the Basic Reference Model or seven-layer model, and a set of specific protocols. The OSI reference model was a major advance in the standardisation of network concepts. It promoted the idea of a consistent model of protocol layers, defining interoperability betwixt network devices and software.
The concept of a seven-layer model was provided by the work of Charles Bachman at Honeywell Information Systems.[9] Various aspects of OSI design evolved from experiences with the NPL network, ARPANET, CYCLADES, EIN, and the International Networking Working Group (IFIP WG6.1). In this model, a networking system was divided into layers. Inside each layer, i or more entities implement its functionality. Each entity interacted directly only with the layer immediately below it and provided facilities for employ by the layer in a higher place it.
The OSI standards documents are available from the ITU-T as the 10.200-serial of recommendations.[10] Some of the protocol specifications were also available as part of the ITU-T X series. The equivalent ISO and ISO/IEC standards for the OSI model were bachelor from ISO. Not all are complimentary of charge.[xi]
OSI was an industry attempt, attempting to get industry participants to agree on mutual network standards to provide multi-vendor interoperability.[12] It was common for large networks to support multiple network protocol suites, with many devices unable to interoperate with other devices because of a lack of common protocols. For a period in the late 1980s and early 1990s, engineers, organizations and nations became polarized over the issue of which standard, the OSI model or the Cyberspace protocol suite, would upshot in the best and well-nigh robust computer networks.[v] [xiii] [14] However, while OSI developed its networking standards in the late 1980s,[15] [16] TCP/IP came into widespread use on multi-vendor networks for internetworking.
The OSI model is even so used as a reference for teaching and documentation;[17] however, the OSI protocols originally conceived for the model did not gain popularity. Some engineers fence the OSI reference model is still relevant to cloud computing.[eighteen] Others say the original OSI model doesn't fit today's networking protocols and have suggested instead a simplified arroyo.[19] [20]
Definitions [edit]
Communication protocols enable an entity in one host to interact with a corresponding entity at the same layer in some other host. Service definitions, like the OSI Model, abstractly describe the functionality provided to an (N)-layer by an (N-ane) layer, where N is one of the vii layers of protocols operating in the local host.
At each level North, ii entities at the communicating devices (layer North peers) commutation protocol data units (PDUs) by ways of a layer N protocol. Each PDU contains a payload, called the service data unit (SDU), along with protocol-related headers or footers.
Data processing past 2 communicating OSI-uniform devices gain as follows:
- The data to be transmitted is composed at the topmost layer of the transmitting device (layer N) into a protocol information unit (PDU).
- The PDU is passed to layer North-ane, where it is known as the service data unit (SDU).
- At layer N-one the SDU is concatenated with a header, a footer, or both, producing a layer Due north-i PDU. Information technology is then passed to layer Due north-2.
- The procedure continues until reaching the lowermost level, from which the data is transmitted to the receiving device.
- At the receiving device the information is passed from the lowest to the highest layer every bit a series of SDUs while being successively stripped from each layer'due south header or footer until reaching the topmost layer, where the concluding of the data is consumed.
Standards documents [edit]
The OSI model was defined in ISO/IEC 7498 which consists of the post-obit parts:
- ISO/IEC 7498-one The Basic Model
- ISO/IEC 7498-ii Security Architecture
- ISO/IEC 7498-3 Naming and addressing
- ISO/IEC 7498-4 Management framework
ISO/IEC 7498-1 is too published as ITU-T Recommendation Ten.200.
Layer compages [edit]
The recommendation X.200 describes seven layers, labelled ane to 7. Layer 1 is the lowest layer in this model.
| Layer | Protocol data unit of measurement (PDU) | Function[21] | ||
|---|---|---|---|---|
| Host layers | 7 | Application | Information | High-level APIs, including resource sharing, remote file admission |
| 6 | Presentation | Translation of information between a networking service and an awarding; including character encoding, data pinch and encryption/decryption | ||
| 5 | Session | Managing communication sessions, i.east., continuous substitution of data in the course of multiple back-and-along transmissions between 2 nodes | ||
| four | Transport | Segment, Datagram | Reliable transmission of information segments between points on a network, including segmentation, acknowledgement and multiplexing | |
| Media layers | 3 | Network | Packet | Structuring and managing a multi-node network, including addressing, routing and traffic command |
| ii | Data link | Frame | Reliable transmission of data frames between two nodes connected by a concrete layer | |
| i | Concrete | Bit, Symbol | Transmission and reception of raw bit streams over a concrete medium | |
Layer 1: Physical layer [edit]
The physical layer is responsible for the transmission and reception of unstructured raw data between a device and a physical transmission medium. It converts the digital bits into electrical, radio, or optical signals. Layer specifications ascertain characteristics such as voltage levels, the timing of voltage changes, physical data rates, maximum transmission distances, modulation scheme, channel access method and concrete connectors. This includes the layout of pins, voltages, line impedance, cable specifications, betoken timing and frequency for wireless devices. Bit rate control is done at the physical layer and may define transmission style as simplex, one-half duplex, and full duplex. The components of a physical layer can be described in terms of a network topology. Physical layer specifications are included in the specifications for the ubiquitous Bluetooth, Ethernet, and USB standards. An example of a less well-known physical layer specification would be for the CAN standard.
Layer 2: Information link layer [edit]
The data link layer provides node-to-node data transfer—a link between 2 directly connected nodes. Information technology detects and perchance corrects errors that may occur in the physical layer. It defines the protocol to establish and terminate a connection betwixt 2 physically connected devices. Information technology also defines the protocol for menstruum command between them.
IEEE 802 divides the data link layer into two sublayers:[22]
- Medium access command (MAC) layer – responsible for controlling how devices in a network proceeds admission to a medium and permission to transmit data.
- Logical link control (LLC) layer – responsible for identifying and encapsulating network layer protocols, and controls error checking and frame synchronization.
The MAC and LLC layers of IEEE 802 networks such as 802.3 Ethernet, 802.11 Wi-Fi, and 802.15.4 ZigBee operate at the data link layer.
The Point-to-Bespeak Protocol (PPP) is a data link layer protocol that can operate over several different physical layers, such as synchronous and asynchronous serial lines.
The ITU-T 1000.hn standard, which provides high-speed local area networking over existing wires (power lines, telephone lines and coaxial cables), includes a complete data link layer that provides both error correction and catamenia control by means of a selective-echo sliding-window protocol.
Security, specifically (authenticated) encryption, at this layer tin be applied with MACSec.
Layer 3: Network layer [edit]
The network layer provides the functional and procedural means of transferring packets from 1 node to another connected in "different networks". A network is a medium to which many nodes can be connected, on which every node has an address and which permits nodes connected to it to transfer messages to other nodes continued to it by but providing the content of a message and the address of the destination node and letting the network find the way to deliver the message to the destination node, possibly routing it through intermediate nodes. If the message is likewise big to exist transmitted from one node to another on the information link layer between those nodes, the network may implement bulletin commitment by splitting the message into several fragments at one node, sending the fragments independently, and reassembling the fragments at another node. It may, but does not need to, written report delivery errors.
Message delivery at the network layer is not necessarily guaranteed to be reliable; a network layer protocol may provide reliable message commitment, but it need not do so.
A number of layer-direction protocols, a function defined in the direction annex, ISO 7498/iv, belong to the network layer. These include routing protocols, multicast group direction, network-layer information and error, and network-layer address assignment. It is the part of the payload that makes these belong to the network layer, not the protocol that carries them.[23]
Layer 4: Ship layer [edit]
The ship layer provides the functional and procedural means of transferring variable-length data sequences from a source to a destination host, while maintaining the quality of service functions.
The transport layer may command the reliability of a given link through period control, segmentation/desegmentation, and fault control. Some protocols are land- and connection-oriented. This ways that the ship layer can go along runway of the segments and retransmit those that fail delivery. The send layer may also provide the acknowledgement of the successful data transmission and sends the adjacent data if no errors occurred. The ship layer creates segments out of the bulletin received from the application layer. Segmentation is the process of dividing a long message into smaller messages.
Reliability, however, is not a strict requirement within the transport layer. Protocols similar UDP, for example, are used in applications that are willing to take some packet loss, reordering, errors or duplication. Streaming media, existent-time multiplayer games and voice over IP (VoIP) are examples of applications in which loss of packets is not usually a fatal problem.
OSI defines v classes of connection-mode send protocols ranging from class 0 (which is too known every bit TP0 and provides the fewest features) to class 4 (TP4, designed for less reliable networks, similar to the Internet). Class 0 contains no mistake recovery and was designed for employ on network layers that provide error-complimentary connections. Course 4 is closest to TCP, although TCP contains functions, such as the graceful close, which OSI assigns to the session layer. Also, all OSI TP connectedness-fashion protocol classes provide expedited data and preservation of record boundaries. Detailed characteristics of TP0-4 classes are shown in the following table:[24]
| Characteristic name | TP0 | TP1 | TP2 | TP3 | TP4 |
|---|---|---|---|---|---|
| Connexion-oriented network | Aye | Aye | Yep | Yes | Yes |
| Connectionless network | No | No | No | No | Yes |
| Concatenation and separation | No | Yes | Yes | Yeah | Yes |
| Segmentation and reassembly | Yes | Yes | Yep | Yes | Yes |
| Error recovery | No | Yes | Yes | Yes | Yes |
| Reinitiate connection a | No | Yeah | No | Aye | No |
| Multiplexing / demultiplexing over single virtual circuit | No | No | Yes | Yes | Yes |
| Explicit period control | No | No | Yes | Yes | Aye |
| Retransmission on timeout | No | No | No | No | Yes |
| Reliable transport service | No | Aye | No | Yes | Yeah |
| a If an excessive number of PDUs are unacknowledged. | |||||
An easy mode to visualize the transport layer is to compare it with a post office, which deals with the dispatch and classification of post and parcels sent. A post part inspects only the outer envelope of mail to determine its delivery. Higher layers may have the equivalent of double envelopes, such as cryptographic presentation services that can be read by the leaseholder only. Roughly speaking, tunnelling protocols operate at the ship layer, such as carrying not-IP protocols such as IBM's SNA or Novell's IPX over an IP network, or end-to-end encryption with IPsec. While Generic Routing Encapsulation (GRE) might seem to be a network-layer protocol, if the encapsulation of the payload takes place only at the endpoint, GRE becomes closer to a transport protocol that uses IP headers just contains complete Layer 2 frames or Layer 3 packets to evangelize to the endpoint. L2TP carries PPP frames inside transport segments.
Although non developed under the OSI Reference Model and not strictly conforming to the OSI definition of the transport layer, the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) of the Internet Protocol Suite are commonly categorized as layer-four protocols within OSI.
Transport Layer Security (TLS) does non strictly fit inside the model either. It contains characteristics of the send and presentation layers.[25] [26]
Layer 5: Session layer [edit]
The session layer controls the dialogues (connections) between computers. It establishes, manages and terminates the connections between the local and remote application. It provides for full-duplex, half-duplex, or simplex operation, and establishes procedures for checkpointing, suspending, restarting, and terminating a session. In the OSI model, this layer is responsible for gracefully endmost a session. This layer is also responsible for session checkpointing and recovery, which is not usually used in the Internet Protocol Suite. The session layer is commonly implemented explicitly in application environments that use remote procedure calls.
In the modernistic TCP/IP arrangement, the session layer is non-existent and is just office of TCP.
Layer 6: Presentation layer [edit]
The presentation layer establishes context between awarding-layer entities, in which the application-layer entities may employ different syntax and semantics if the presentation service provides a mapping between them. If a mapping is available, presentation protocol data units are encapsulated into session protocol data units and passed downward the protocol stack.
This layer provides independence from data representation by translating betwixt application and network formats. The presentation layer transforms information into the class that the application accepts. This layer formats data to exist sent beyond a network. Information technology is sometimes chosen the syntax layer.[27] The presentation layer can include pinch functions.[28] The Presentation Layer negotiates the Transfer Syntax.
The original presentation structure used the Bones Encoding Rules of Abstract Syntax Notation One (ASN.1), with capabilities such as converting an EBCDIC-coded text file to an ASCII-coded file, or serialization of objects and other information structures from and to XML. ASN.1 finer makes an awarding protocol invariant with respect to syntax.
Layer 7: Application layer [edit]
The application layer is the OSI layer closest to the end user, which means both the OSI application layer and the user collaborate straight with the software awarding. This layer interacts with software applications that implement a communicating component. Such application programs fall exterior the scope of the OSI model. Application-layer functions typically include identifying communication partners, determining resource availability, and synchronizing advice. When identifying communication partners, the application layer determines the identity and availability of communication partners for an application with information to transmit. The near important distinction in the application layer is the distinction between the application-entity and the application. For example, a reservation website might have ii application-entities: one using HTTP to communicate with its users, and one for a remote database protocol to record reservations. Neither of these protocols have anything to exercise with reservations. That logic is in the application itself. The application layer has no means to determine the availability of resource in the network.
Cantankerous-layer functions [edit]
Cross-layer functions are services that are not tied to a given layer, only may affect more than one layer.[29] Some orthogonal aspects, such equally direction and security, involve all of the layers (Meet ITU-T X.800 Recommendation[30]). These services are aimed at improving the CIA triad—confidentiality, integrity, and availability—of the transmitted data. Cross-layer functions are the norm, in exercise, because the availability of a communication service is determined by the interaction betwixt network design and network management protocols.
Specific examples of cross-layer functions include the following:
- Security service (telecommunication)[30] as divers by ITU-T X.800 recommendation.
- Direction functions, i.e. functions that permit to configure, instantiate, monitor, cease the communications of two or more entities: there is a specific application-layer protocol, common management information protocol (CMIP) and its corresponding service, common management information service (CMIS), they demand to collaborate with every layer in order to bargain with their instances.
- Multiprotocol Label Switching (MPLS), ATM, and X.25 are 3a protocols. OSI subdivides the Network Layer into three sublayers: 3a) Subnetwork Access, 3b) Subnetwork Dependent Convergence and 3c) Subnetwork Independent Convergence.[31] It was designed to provide a unified data-carrying service for both excursion-based clients and packet-switching clients which provide a datagram-based service model. Information technology can be used to carry many different kinds of traffic, including IP packets, as well as native ATM, SONET, and Ethernet frames. Sometimes ane sees reference to a Layer 2.5.
- Cantankerous MAC and PHY Scheduling is essential in wireless networks because of the fourth dimension-varying nature of wireless channels. By scheduling packet transmission simply in favourable channel conditions, which requires the MAC layer to obtain channel state data from the PHY layer, network throughput can be significantly improved and free energy waste product can exist avoided.[32]
Programming interfaces [edit]
Neither the OSI Reference Model, nor any OSI protocol specifications, outline any programming interfaces, other than deliberately abstract service descriptions. Protocol specifications define a methodology for communication between peers, merely the software interfaces are implementation-specific.
For example, the Network Commuter Interface Specification (NDIS) and Open Data-Link Interface (ODI) are interfaces between the media (layer 2) and the network protocol (layer 3).
Comparison to other networking suites [edit]
The table below presents a list of OSI layers, the original OSI protocols, and some judge modern matches. Information technology is very important to note that this correspondance is crude: the OSI model contains idiosyncracies not found in later systems such equally the IP stack in modern Cyberspace.[20]
| Layer | OSI protocols | TCP/IP protocols | Signaling System vii[33] | AppleTalk | IPX | SNA | UMTS | Miscellaneous examples | |
|---|---|---|---|---|---|---|---|---|---|
| No. | Name | ||||||||
| 7 | Application |
|
|
|
|
|
|
| |
| vi | Presentation |
|
|
|
| ||||
| five | Session |
| Sockets (session institution in TCP / RTP / PPTP) |
|
|
|
| ||
| 4 | Transport |
|
|
|
|
| |||
| three | Network |
|
|
| ATP (TokenTalk / EtherTalk) |
|
|
|
|
| 2 | Data link |
|
|
|
| IEEE 802.3 framing Ethernet Two framing |
|
|
|
| 1 | Physical |
| TCP/IP stack does non care nearly the physical medium, as long as it provides a style to communicate octets |
|
|
| UMTS air interfaces |
| |
Comparison with TCP/IP model [edit]
The design of protocols in the TCP/IP model of the Internet does not business organization itself with strict hierarchical encapsulation and layering.[38] RFC 3439 contains a section entitled "Layering considered harmful".[39] TCP/IP does recognize four broad layers of functionality which are derived from the operating scope of their contained protocols: the scope of the software application; the host-to-host send path; the internetworking range; and the scope of the direct links to other nodes on the local network.[40]
Despite using a different concept for layering than the OSI model, these layers are often compared with the OSI layering scheme in the following way:
- The Cyberspace application layer maps to the OSI application layer, presentation layer, and nigh of the session layer.
- The TCP/IP transport layer maps to the graceful close function of the OSI session layer equally well as the OSI transport layer.
- The internet layer performs functions as those in a subset of the OSI network layer.
- The link layer corresponds to the OSI data link layer and may include similar functions as the physical layer, as well as some protocols of the OSI'southward network layer.
These comparisons are based on the original vii-layer protocol model as defined in ISO 7498, rather than refinements in the internal arrangement of the network layer.
The OSI protocol suite that was specified as part of the OSI project was considered past many as also complicated and inefficient, and to a large extent unimplementable.[41] Taking the "forklift upgrade" approach to networking, it specified eliminating all existing networking protocols and replacing them at all layers of the stack. This made implementation difficult and was resisted past many vendors and users with significant investments in other network technologies. In addition, the protocols included and so many optional features that many vendors' implementations were non interoperable.[41]
Although the OSI model is frequently withal referenced, the Internet protocol suite has get the standard for networking. TCP/IP's pragmatic approach to calculator networking and to independent implementations of simplified protocols fabricated it a practical methodology.[41] Some protocols and specifications in the OSI stack remain in use, 1 case existence IS-IS, which was specified for OSI as ISO/IEC 10589:2002 and adjusted for Cyberspace use with TCP/IP every bit RFC 1142.
Come across also [edit]
- Mutual Management Data Service (CMIS)
- GOSIP, the (U.S.) Government Open up Systems Interconnection Profile
- Hierarchical internetworking model
- Layer 8
- List of information technology initialisms
- Direction plane
- Recursive Internetwork Architecture
- Service layer
Further reading [edit]
- John Twenty-four hours, "Patterns in Network Architecture: A Return to Fundamentals" (Prentice Hall 2007, ISBN 978-0-xiii-225242-iii)
- Marshall Rose, "The Open Volume" (Prentice-Hall, Englewood Cliffs, 1990)
- David M. Piscitello, A. Lyman Chapin, Open Systems Networking (Addison-Wesley, Reading, 1993)
- Andrew S. Tanenbaum, Figurer Networks, 4th Edition, (Prentice-Hall, 2002) ISBN 0-xiii-066102-3
- Gary Dickson; Alan Lloyd (July 1992). Open up Systems Interconnection/Figurer Communications Standards and Gossip Explained. Prentice-Hall. ISBN978-0136401117.
References [edit]
- ^ "X.225 : Information engineering science – Open Systems Interconnection – Connection-oriented Session protocol: Protocol specification". Archived from the original on one February 2021. Retrieved 24 November 2021.
- ^ a b Davies, Howard; Bressan, Beatrice (26 Apr 2010). A History of International Research Networking: The People who Made information technology Happen. John Wiley & Sons. pp. 2–3. ISBN978-iii-527-32710-ii.
- ^ Roberts, Dr. Lawrence Grand. (Nov 1978). "The Development of Packet Switching" (PDF). IEEE Invited Paper . Retrieved 26 February 2022.
- ^ Down, Peter John; Taylor, Frank Edward (1976). Why distributed calculating?: An NCC review of potential and feel in the UK. NCC Publications. ISBN9780850121704.
- ^ a b Andrew 50. Russell (30 July 2013). "OSI: The Internet That Wasn't". IEEE Spectrum. Vol. l, no. 8.
- ^ "OSI The Cyberspace That Wasn't". IEEE Spectrum. March 2017.
- ^ Sunshine, Carl A. (1989). Computer Network Architectures and Protocols. Springer Science & Business Media. p. 35. ISBN978-1-4613-0809-6.
- ^ Hasman, A. (1995). Education and Preparation in Health Information science in Europe: Land of the Fine art, Guidelines, Applications. IOS Printing. p. 251. ISBN978-90-5199-234-2.
- ^ J. A. N. Lee. "Computer Pioneers by J. A. N. Lee". IEEE Reckoner Society.
- ^ "ITU-T X-Series Recommendations".
- ^ "Publicly Available Standards". Standards.iso.org. 30 July 2010. Retrieved 11 September 2010.
- ^ Russell, Andrew Fifty. (28 April 2014). Open Standards and the Digital Historic period: History, Ideology, and Networks. Cambridge Academy Press. ISBN978-1-139-91661-5.
- ^ Russell, Andrew 50. "Rough Consensus and Running Code' and the Internet-OSI Standards State of war" (PDF). IEEE Annals of the History of Computing.
- ^ "Standards Wars" (PDF). 2006.
- ^ Inc, IDG Network World (15 February 1988). Network World. IDG Network Earth Inc.
- ^ Inc, IDG Network World (10 October 1988). Network World. IDG Network Globe Inc.
- ^ Shaw, Keith (22 Oct 2018). "The OSI model explained: How to understand (and remember) the 7 layer network model". Network World . Retrieved 16 May 2020.
- ^ "An OSI Model for Cloud". Cisco Blogs. 24 February 2017. Retrieved 16 May 2020.
- ^ Taylor, Steve; Metzler, Jim (23 September 2008). "Why it's time to allow the OSI model die". Network Globe . Retrieved 16 May 2020.
- ^ a b Crawford, JB (27 March 2021). "The actual OSI model".
- ^ "Windows Network Architecture and the OSI Model". Microsoft Documentation . Retrieved 24 June 2020.
- ^ "five.2 RM description for end stations". IEEE Std 802-2014, IEEE Standard for Local and Metropolitan Area Networks: Overview and Architecture . ieee. doi:ten.1109/IEEESTD.2014.6847097. ISBN978-0-7381-9219-2.
- ^ International Organization for Standardization (xv November 1989). "ISO/IEC 7498-four:1989 -- Information engineering science -- Open Systems Interconnection -- Basic Reference Model: Naming and addressing". ISO Standards Maintenance Portal. ISO Central Secretariat. Retrieved 17 August 2015.
- ^ "ITU-T Recommendation X.224 (11/1995) ISO/IEC 8073, Open up Systems Interconnection - Protocol for providing the connection-mode transport service". ITU.
- ^ Hooper, Howard (2012). CCNP Security VPN 642-648 Official Cert Guide (2 ed.). Cisco Press. p. 22. ISBN9780132966382.
- ^ Spott, Andrew; Leek, Tom; et al. "What layer is TLS?". Information Security Stack Commutation.
- ^ Grigonis, Richard (2000). Computer telephony- encyclopaedia. CMP. p. 331. ISBN9781578200450.
- ^ "ITU-T 10.200 - Information engineering – Open up Systems Interconnection – Basic Reference Model: The basic model".
- ^ Mao, Stephen (xiii November 2009). "Chapter 8: Fundamentals of communication networks". In Wyglinski, Alexander; Nekovee, Maziar; Hou, Thomas (eds.). Cognitive Radio Communications and Networks: Principles and Practice. Elsevier. p. 201. ISBN978-0-08-087932-1.
- ^ a b "ITU-T Recommendation X.800 (03/91), Security compages for Open up Systems Interconnection for CCITT applications". ITU. Retrieved fourteen August 2015.
- ^ Hegering, Heinz-Gerd (24 August 1999). Integrated management of networked systems : concepts, architectures, and their operational application. Morgan Kaufmann. p. 54. ISBN978-1558605718.
- ^ Miao, Guowang; Song, Guocong (2014). Energy and spectrum efficient wireless network design. Cambridge University Printing. ISBN978-1107039889.
- ^ "ITU-T Recommendation Q.1400 (03/1993)], Architecture framework for the development of signaling and OA&Thou protocols using OSI concepts". ITU. pp. 4, vii.
- ^ ITU Rec. X.227 (ISO 8650), X.217 (ISO 8649).
- ^ 10.700 series of recommendations from the ITU-T (in particular X.711) and ISO 9596.
- ^ a b "Internetworking Engineering science Handbook - Internetworking Nuts [Internetworking]". Cisco. 15 January 2014. Retrieved xiv August 2015.
- ^ "3GPP specification: 36.300". 3gpp.org . Retrieved 14 August 2015.
- ^ RFC 3439
- ^ "RFC 3439 - Some Net Architectural Guidelines and Philosophy". ietf.org . Retrieved 14 August 2015.
- ^ Walter Goralski (2009). The Illustrated Network: How TCP/IP Works in a Modern Network (PDF). Morgan Kaufmann. p. 26. ISBN978-0123745415.
- ^ a b c Andrew S. Tanenbaum, Estimator Networks, § 1.four.4.
External links [edit]
| | Wikimedia Commons has media related to OSI model. |
- Microsoft Noesis Base: The OSI Model'southward Vii Layers Defined and Functions Explained
- ISO/IEC standard 7498-1:1994 (PDF certificate inside ZIP annal) (requires HTTP cookies in club to accept licence agreement)
- ITU-T X.200 (the same contents as from ISO)
- "Information CHanGe Architectures and Menstruation Charts powered past Google App Engine". infchg.appspot.com. The ISO OSI Reference Model, Beluga graph of information units and groups of layers. Archived from the original on 26 May 2012.
{{cite web}}: CS1 maint: others (link) - Zimmermann, Hubert (April 1980). "OSI Reference Model — The ISO Model of Architecture for Open up Systems Interconnection". IEEE Transactions on Communications. 28 (4): 425–432. CiteSeerX10.one.one.136.9497. doi:ten.1109/TCOM.1980.1094702. S2CID 16013989.
- Cisco Systems Internetworking Technology Handbook
Which Protocol Header Would Layer 4 Device Read and Process
Source: https://en.wikipedia.org/wiki/OSI_model